Automated Malware Incident Response and Analysis
Project description
AMIRA: Automated Malware Incident Response & Analysis
AMIRA is a service for automatically running the analysis on the OSXCollector output files. The automated analysis is performed via OSXCollector Output Filters, in particular The One Filter to Rule Them All: the Analyze Filter. AMIRA takes care of retrieving the output files from an S3 bucket, running the Analyze Filter and then uploading the results of the analysis back to S3 (although one could envision as well attaching them to the related JIRA ticket).
Prerequisites
tox
The following steps assume you have tox installed on your machine.
If this is not the case, please run:
$ sudo pip install tox
OSXCollector Output Filters configuration file
AMIRA uses OSXCollector Output Filters to do the actual analysis,
so you will need to have a valid osxcollector.yaml
configuration file in the working directory.
The example configuration file can be found in the
OSXCollector Output Filters.
The configuration file mentions the location of the file hash and the domain blacklists. Make sure that the blacklist locations mentioned in the configuration file are also available when running AMIRA.
AWS credentials
AMIRA uses boto to interface with AWS. You can supply the credentials using either of the possible boto config files.
The credentials should allow reading and deleting SQS messages from the SQS queue specified in the AMIRA config as well as the read access to the objects in the S3 bucket where the OSXCollector output files are stored. To be able to upload the analysis results back to the S3 bucket specified in the AMIRA configuration file, the credentials should also allow write access to this bucket.
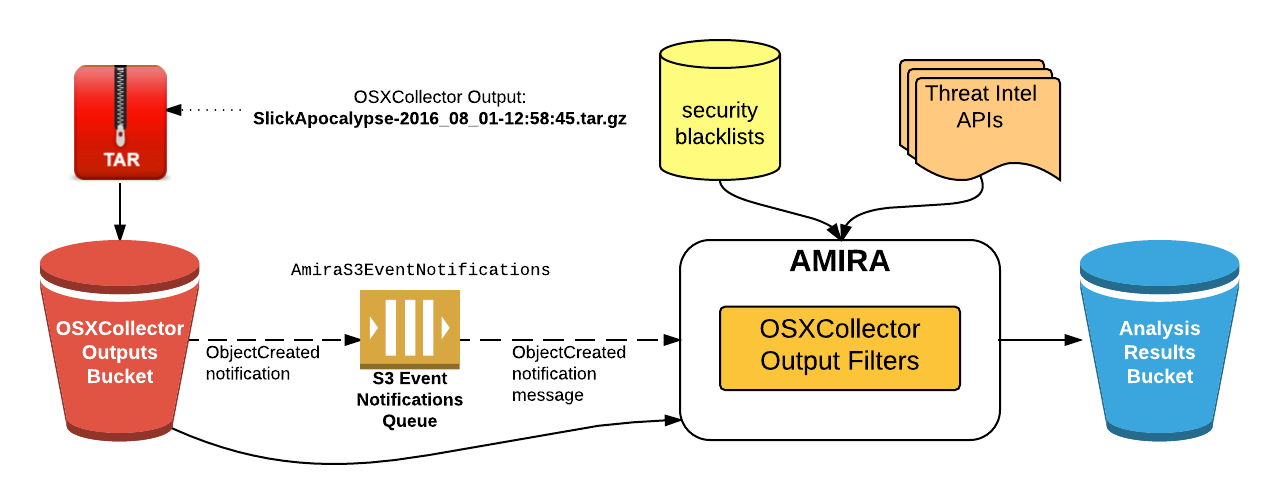
AMIRA Architecture
The service uses the
S3 bucket event notifications
to trigger the analysis.
You will need to configure an S3 bucket for the OSXCollector output files,
so that when a file is added there the notification will be sent to an SQS queue
(AmiraS3EventNotifications in the picture below).
AMIRA periodically checks the queue for any new messages
and upon receiving one it will fetch the OSXCollector output file from the S3
bucket.
It will then run the Analyze Filter on the retrieved file.
The Analyze Filter runs all the filters contained in the OSXCollector Output Filters package sequentially. Some of them communicate with the external resources, like domain and hashes blacklists (or whitelists) and threat intel APIs, e.g. VirusTotal, OpenDNS Investigate or ShadowServer. The original OSXCollector output is extended with all of this information and the very last filter run by the Analyze Filter summarizes all of the findings into a human-readable form. After the filter finishes running, the results of the analysis will be uploaded to the Analysis Results S3 bucket.
The overview of the whole process and the system components involved in it are depicted below:
Using AMIRA
The main entry point to AMIRA is in the amira/amira.py module.
You will first need to create an instance of AMIRA class by providing the AWS
region name, where the SQS queue with the event notifications for the
OSXCollector output bucket is, and the SQS queue name:
from amira.amira import AMIRA
amira = AMIRA('us-west-1', 'AmiraS3EventNotifications')
Then you can register the analysis results uploader, e.g. the S3 results uploader:
from amira.s3 import S3ResultsUploader
s3_results_uploader = S3ResultsUploader('amira-results-bucket')
amira.register_results_uploader(s3_results_uploader)
Finally, run AMIRA:
amira.run()
Go get some coffee, sit back, relax and wait till the analysis results pop up in the S3 bucket!
Project details
Release history Release notifications | RSS feed
Download files
Download the file for your platform. If you're not sure which to choose, learn more about installing packages.
Source Distribution
Built Distribution
File details
Details for the file amira-1.1.0.tar.gz.
File metadata
- Download URL: amira-1.1.0.tar.gz
- Upload date:
- Size: 7.9 kB
- Tags: Source
- Uploaded using Trusted Publishing? No
- Uploaded via: twine/1.13.0 pkginfo/1.5.0.1 requests/2.21.0 setuptools/40.9.0 requests-toolbelt/0.9.1 tqdm/4.31.1 CPython/2.7.14
File hashes
| Algorithm | Hash digest | |
|---|---|---|
| SHA256 | 33f4eec103e911830a11f3f3c45db918164f752f0938af05f4afd5b43a94e18c |
|
| MD5 | 488593e40ef730963053d16ee3f7da26 |
|
| BLAKE2b-256 | 76b7b866900afb206c0488d0fa4c314d9d22a2bd4d3d306d40df8623c8250287 |
File details
Details for the file amira-1.1.0-py2-none-any.whl.
File metadata
- Download URL: amira-1.1.0-py2-none-any.whl
- Upload date:
- Size: 9.4 kB
- Tags: Python 2
- Uploaded using Trusted Publishing? No
- Uploaded via: twine/1.13.0 pkginfo/1.5.0.1 requests/2.21.0 setuptools/40.9.0 requests-toolbelt/0.9.1 tqdm/4.31.1 CPython/2.7.14
File hashes
| Algorithm | Hash digest | |
|---|---|---|
| SHA256 | 24da8c60bff2d820684b63a5885f0f3b87b8e96f43c0775e3f3ca604b247bcfa |
|
| MD5 | faeb5e9dab12fb9efad2d0de3ef197a4 |
|
| BLAKE2b-256 | 2a1a7c51f694baad38e4dfb6eed8f894ca8b5fa491cb83a38c0faa9026d15080 |