Two-step verification for Plone 4 using the Google Authenticator app.
Project description
Two-step verification for Plone 4 with use of Google Authenticator app. This app allows users to enable the two-step verification for their Plone accounts. A mobile device with Google Authenticator app installed is required. Usage of two-step verification is optonal, unless site admins have forced it (configurable in app control panel). Admins can white-list the IPs, for which the two-step verification would be skipped.
Prerequiresites
GoogleAuthenticator app installed on mobile device (official app available for Android, iPhone and Blackberry; third-party app exists for Windows Phone).
Plone 4 (tested with Plone >= 4.2.6)
Usage
Case 1: Enabling the two-step verification
Pre-conditions: User is not logged into the Plone site, does not yet have two-step verification enabled and has installed the Google Authenticator app (including the advised bar code scanner) on his mobile device.
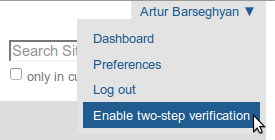
From any page follow the “Enable two-step verification” link in the menu (next to “Log out”).
That will bring you to a page on which a bar code is shown.
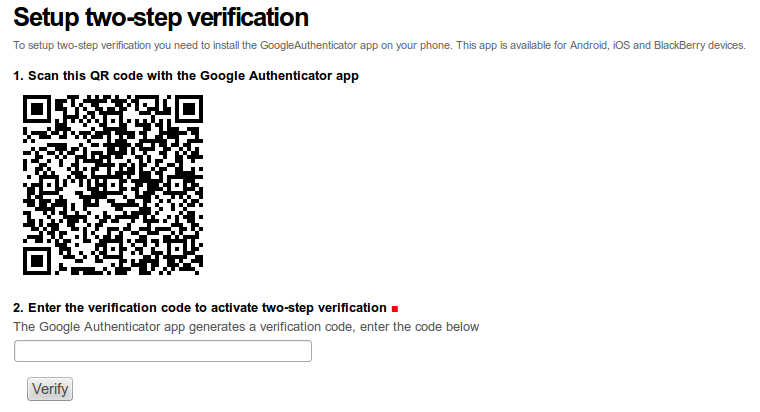
You’re supposed to scan the bar code shown on the page using the bar code scanner installed on your mobile device, which you’re going to use for verification.
After you have successfully scanned the bar code, enter the token shown in the “Enter the verification code to activate two-step verification” field for confirmation and press the “Verify” button.
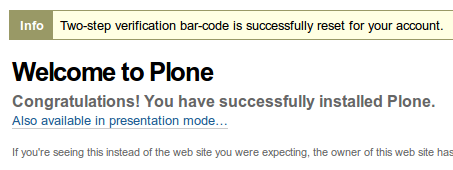
Upon successful confirmation (you should see a message stating that) the two-step verification is enabled for your account.
Case 2: Two-step verification
Pre-conditions: User is not logged in and has enabled the two-step verification.
When you log into the Plone site (just using username and password), you would see an extra screen on which you are asked to provide the token, generated by Google Authenticator.
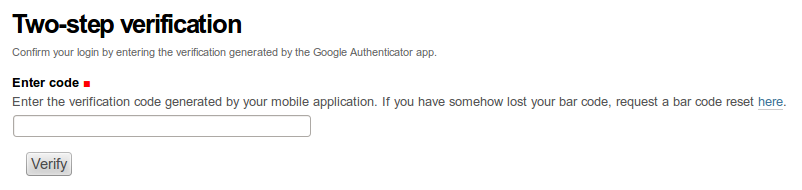
You should then open the Google Authenticator app on your mobile device and type in the token shown into the “Enter code” field.
If token is valid, you would be logged in.
Case 3: Lost tokens
Pre-conditions: User is not logged in, has enabled the two-step verification.
There might be cases when you have lost your token (either removed it from your app by accident or lost the mobile device). For such cases, you can reset the bar code.
Log into the Plone site (just using username and password), for to see the extra screen on which you are asked to provide the token, generated by Google Authenticator and follow the link (help text of the “Enter code” field). You would then land on the page where from you can request the bar code reset.
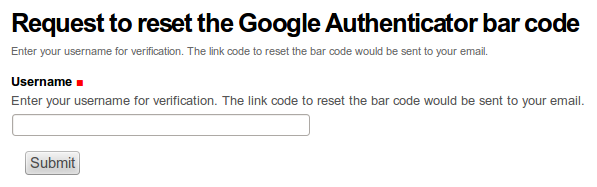
Enter your username in the “Username” field, press the “Submit” button. Link for resetting your bar code appear in your mailbox shortly. Having clicked on the link to reset the bar code, would bring your to a page where you can scan the bar-code same way you have done it when setting up the two-step verification.
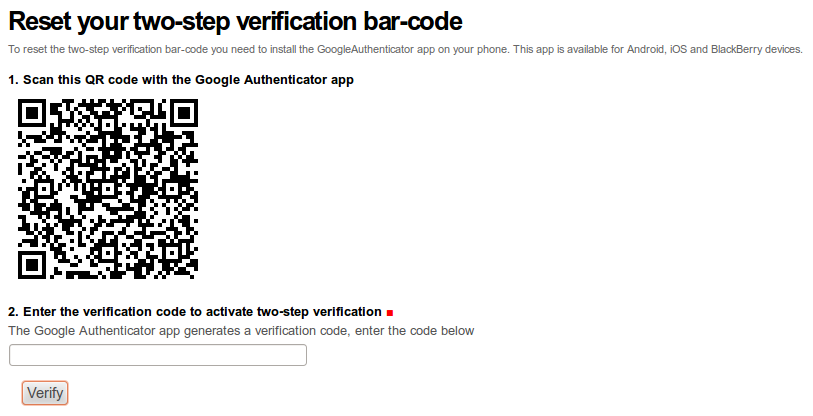
Scan the code with your mobile device and enter the code in the “Enter the verification code to activate the two-step verification” field.
Upon successful confirmation (you should see a message stating that) your bar code is reset.
Case 4: Disabling the two-step verification
Pre-conditions: User is logged in and has enabled the two-step verification.
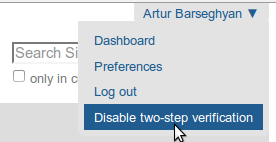
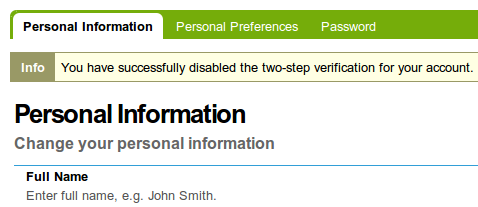
From any page follow the “Disable two-step verification” link in the menu (next to “Log out”).
After which you would get a message.
Installation
Buildout
>>> [instance] >>> eggs += >>> collective.googleauthenticator
>>> zcml += >>> collective.googleauthenticator
ZMI
ZMI -> portal_quickinstaller
Choose “Google Authenticator Plone” and install it.
ZMI -> acl_users
Choose “google_auth (Google Authenticator plugin (collective.googleauthenticator))”.
Make sure the “Active plugins” section of “Authentication” has the following plugins in the given order (“google_auth” should come as first - critical!):
google_auth
session
source_users
Configuration options
App control panel can be accessed at http://your-plone-site.com/@@google-authenticator-settings

Secret Key
Site secret key - can be any string. See it as some sort of a password.
Globally enabled
If checked, two-step verification is globally force-enabled for all site users and they no longer have an option to disable it; this applies to all new users (just registered accounts) as well.
White-listed IP addresses
List of white-listed IP addresses - one at a line. If user comes from one of those, the two-step verification is skipped even if user has enabled it or two-step verification is globally enabled.
Extra
Additionals options of the control panel are:
Enable two-step verification for all users.
Disable two-step verification for all users.
Notes
It’s important that Google Authenticator comes as first in the ZMI -> acl_users -> Authentication.
Tested in combination with the following products:
The Products.LoginLockout. GoogleAuthenticator comes as first, LoginLockout as second. All works fine.
Implementation details
This package is beta. Comments and suggestions are welcome.
Plone PAS plugin, which checks if user has the two-step verification enabled for user trying to log in. If so, redirect user to a separate page (a view), where the extra credentials (Google Authenticator token) is asked for.
Google Authenticator token validation form view. If token is valid, definitely authenticates the user.
Google Authenticator setup form view, where each user scans a bar code image is shown and fills in the token generated by his Google Authenticator app. Upon successful token validation, the two-step verification is enabled for the user.
- User record is extended with two fields:
enable_two_factor_authentication (bool): Indicates whether user has enabled the two-step verification for his profile.
two_factor_authentication_secret (str): Users’ secret key to be used for generating the bar code image. Filled in automatically when user enables the two-step verification.
Google Authenticator disable view, on which user can disable the two-step verification for his account.
The Plone standard login form (skins/login_form.cpt) has been overridden (the came_from form field taken out). Still the “came from” functionality works still in the very same way as it was before, just slightly different - in a way that it works well with Google Authenticator too.
The Plone standard “popupforms.js” has been overridden. The part of login forms being shown in an overlay has been taken out, due to the problems of Google Authenticator working with overlays. This issue might be solved in future versions of the app.
Documentation
See the documentation at:
Troubleshooting
If you’re quick enough to enter the tokens generated by GoogleAuthenticator app before they expire (remaining time is clearly indicated in the GoogleAuthenticator app) but still get the “Invalid token or token expired” message, make sure your timezone settings on the server are accurate.
Support
For feature requests or bugs, open an issue. For questions, send us an email to info@gw20e.com.
License
GPL 2.0
TODOs and Roadmap
See TODOS.rst file for the list of TODOs.
Changelog
0.2.5
20-06-2014
Improved PAS plugin.
0.2.4
30-01-2014
Minor fixes.
0.2.3
29-01-2014
Making sure the URL to reset the bar-code in template is not escaped.
0.2.2
29-01-2014
Send e-mail in “text/html” format for requst bar code reset template.
0.2.1
29-01-2014
Fix typo in helpers.extract_ip_address_from_request (proxy related).
0.2
23-01-2014
Now admins are able to force the two-step verification for all users (app control panel).
Omit two-step verification for white-listed IP addresses (app control panel).
Links to enable/disable two-step verification moved from “Personal preferences” page to Plone menu (next to “Log out”).
0.1.1
15-01-2014
Fixes in manifest.
0.1
13-01-2014
Initial release (no longer available on PyPI), with two-step verification, bar-code/token recover, basic app control panel.
Project details
Download files
Download the file for your platform. If you're not sure which to choose, learn more about installing packages.
Source Distribution
File details
Details for the file collective.googleauthenticator-0.2.5.tar.gz.
File metadata
- Download URL: collective.googleauthenticator-0.2.5.tar.gz
- Upload date:
- Size: 38.1 kB
- Tags: Source
- Uploaded using Trusted Publishing? No
File hashes
| Algorithm | Hash digest | |
|---|---|---|
| SHA256 | 087dfbf88f7978c6b7645fe56b7413a8b6e3237f22fa3fff8d4819feda467fc4 |
|
| MD5 | 6e3563f7cfab0bb8eeb6a173758016ae |
|
| BLAKE2b-256 | e1a958ab1804390efc53a44caf701321c54a46ae6910e9cb30947c1f31178267 |












