An authorization library that supports access control models like ACL, RBAC, ABAC in Django
Project description
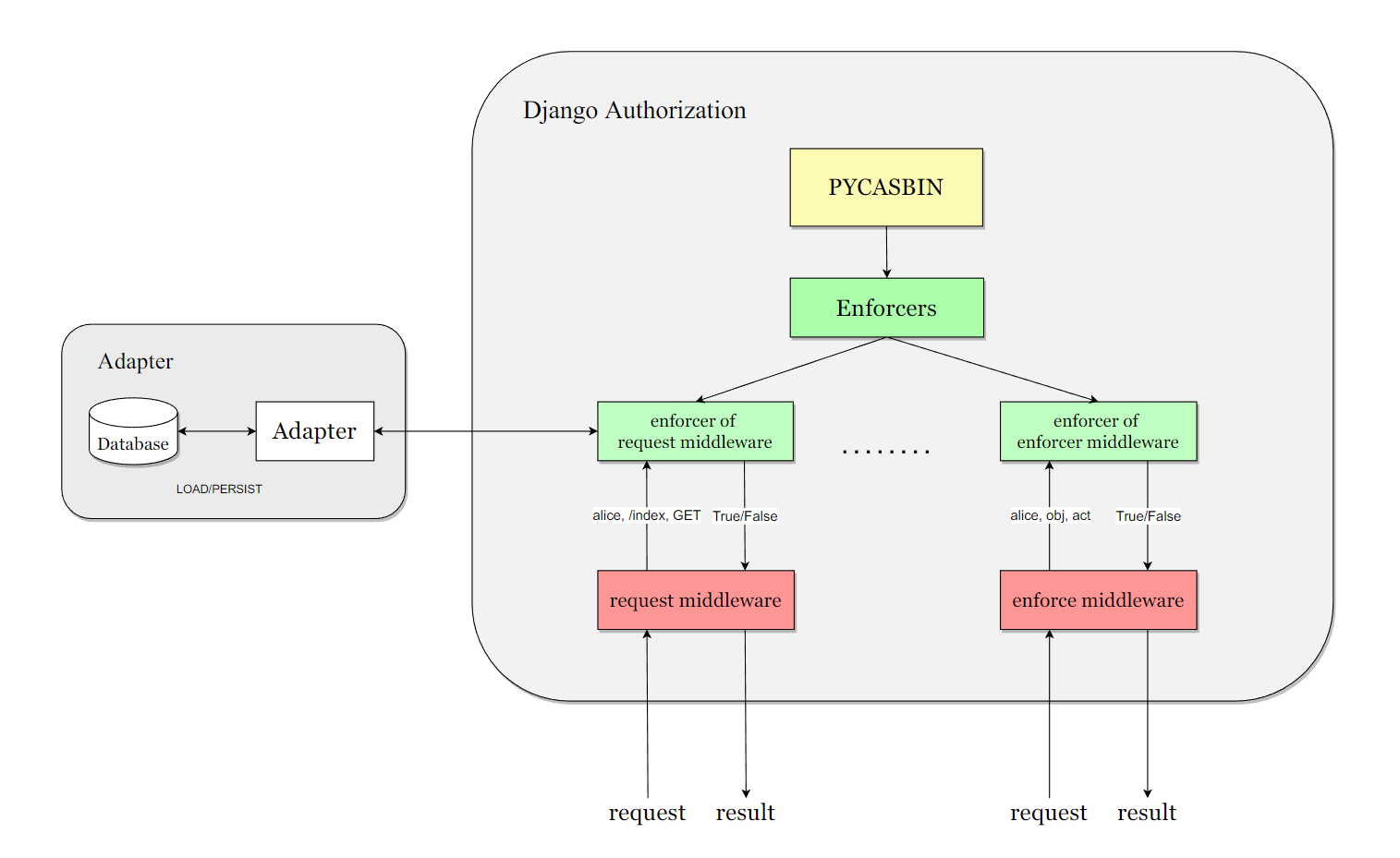
Django Authorization
django-casbin-auth is an authorization library for Django framework.
Based on Casbin and Django-casbin (middleware, light weight of this plugin), an authorization library that that supports access control models like ACL, RBAC, ABAC.
Installation and Configure
pip install django-casbin-auth
We recommend that you first configure the adapter for persistent storage of the policy, such as:
django-orm-adapter, After integrating it into the project continue with the configuration of django-authrization
# 1. Add the app to INSTALLED_APPS
INSTALLED_APPS = [
"django.contrib.admin",
"django.contrib.auth",
"django.contrib.contenttypes",
"django.contrib.sessions",
"django.contrib.messages",
"django.contrib.staticfiles",
"dauthz.apps.DauthzConfig", # add this app to INSTALLED_APPS
]
# 2. Add configure of dauthz
DAUTHZ = {
# DEFAULT Dauthz enforcer
"DEFAULT": {
# Casbin model setting.
"MODEL": {
# Available Settings: "file", "text"
"CONFIG_TYPE": "file",
"CONFIG_FILE_PATH": Path(__file__).parent.joinpath("dauthz-model.conf"),
"CONFIG_TEXT": "",
},
# Casbin adapter .
"ADAPTER": {
"NAME": "casbin_adapter.adapter.Adapter",
# 'OPTION_1': '',
},
"LOG": {
# Changes whether Dauthz will log messages to the Logger.
"ENABLED": False,
},
},
}
to better prompt the configure method of django-casbin-auth, we made a django-app based on django-casbin-auth, you can see it in django-casbin-auth-example
Usage
Some Important Concepts:
such as .conf file, policy, sub, obj, act, please refer to the casbin website
Middleware Usage
# Install middleware for django-casbin-auth as required
MIDDLEWARE = [
"django.middleware.security.SecurityMiddleware",
"django.contrib.sessions.middleware.SessionMiddleware",
"django.middleware.common.CommonMiddleware",
"django.middleware.csrf.CsrfViewMiddleware",
"django.contrib.auth.middleware.AuthenticationMiddleware",
"django.contrib.messages.middleware.MessageMiddleware",
"django.middleware.clickjacking.XFrameOptionsMiddleware",
"dauthz.middlewares.request_middleware.RequestMiddleware", # add the middleware
]
You can freely set the casbin enforcer for the middleware via API: set_enforcer_for_request_middleware(enforcer_name) and set_enforcer_for_enforcer_middleware(enforcer_name)
Decorator Usage
Request decorator will check the authorization status of user, path, method
# use request decorator
@request_decorator
def some_view(request):
return HttpResponse("Hello World")
Enforcer decorator will check the authorization status of user, obj, edit. example:
# use enforcer decorator
# sub: user in request obj: "artical" act: "edit"
@enforcer_decorator("artical", "edit")
def some_view(request):
return HttpResponse("Hello World")
Command Line Usage
The command line operation allows you to operate directly on the enforcer's database. Three sets of commands are available: policy commands, group commands and role commands.
Add/Get policy, usage:
python manage.py policy [opt: --enforcer=<enforcer_name>] add <sub> <obj> <act>
python manage.py policy [opt: --enforcer=<enforcer_name>] get <sub> <obj> <act>
Add/Get role to user, usage:
python manage.py role [opt: --enforcer=<enforcer_name>] add <user> <role>
python manage.py role [opt: --enforcer=<enforcer_name>] get <user>
Add/Get group policy, usage:
python manage.py group [opt: --enforcer=<enforcer_name>] add <user> <role> [opt:<domain>]
python manage.py group [opt: --enforcer=<enforcer_name>] get <user> <role> [opt:<domain>]
Backend Usage
You can integrate Pycasbin with Django authentication system. For more usage, you can refer to tests/test_backend.py. To enable the backend, you need to specify it in settings.py.
AUTHENTICATION_BACKENDS = [
"dauthz.backends.CasbinBackend",
"django.contrib.auth.backends.ModelBackend",
]
Note that you still need to add permissions for users with pycasbin add_policy() due to the mechanism of the django permission system.
License
This project is licensed under the Apache 2.0 license.
Project details
Release history Release notifications | RSS feed
Download files
Download the file for your platform. If you're not sure which to choose, learn more about installing packages.
Source Distribution
Built Distribution
File details
Details for the file django_casbin_auth-1.4.0.tar.gz.
File metadata
- Download URL: django_casbin_auth-1.4.0.tar.gz
- Upload date:
- Size: 3.1 MB
- Tags: Source
- Uploaded using Trusted Publishing? No
- Uploaded via: twine/5.1.1 CPython/3.9.13
File hashes
| Algorithm | Hash digest | |
|---|---|---|
| SHA256 | 1fcdf1cd338566b4690c68414619958f7ef2607ee77900042162cfc6a4208df5 |
|
| MD5 | c4263c1bdf9bf3b52b5e325ccc6c7da1 |
|
| BLAKE2b-256 | 529d71767554dab3f53010e18739e68706ff4eb4c47c9e84badd68f2a66f210e |
File details
Details for the file django_casbin_auth-1.4.0-py3-none-any.whl.
File metadata
- Download URL: django_casbin_auth-1.4.0-py3-none-any.whl
- Upload date:
- Size: 3.8 MB
- Tags: Python 3
- Uploaded using Trusted Publishing? No
- Uploaded via: twine/5.1.1 CPython/3.9.13
File hashes
| Algorithm | Hash digest | |
|---|---|---|
| SHA256 | 16dcf2a9d06b9b00fe59368b484cf37680d6e4345c3cb0354220ba7b06111bdd |
|
| MD5 | a2af8aa3c3b8ee6ee0d67b63ee474b24 |
|
| BLAKE2b-256 | 3ab80143eb13f4f405dd0bc5ea78b8205e6473425eeebff3491b6e87d58ec52f |