Lightweight static analysis for many languages. Find bug variants with patterns that look like source code.
Project description
Code scanning at ludicrous speed.
Semgrep is a fast, open-source, static analysis engine for finding bugs, detecting vulnerabilities in third-party dependencies, and enforcing code standards. Semgrep analyzes code locally on your computer or in your build environment: code is never uploaded. Get started →.
Language support
Semgrep supports 30+ languages.
| Category | Languages |
|---|---|
| GA | C# · Go · Java · JavaScript · JSX · JSON · PHP · Python · Ruby · Scala · Terraform · TypeScript · TSX |
| Beta | Kotlin · Rust |
| Experimental | Bash · C · C++ · Clojure · Dart · Dockerfile · Elixir · HTML · Jsonnet · Lisp · Lua · OCaml · R · Scheme · Solidity · Swift · YAML · XML · Generic (ERB, Jinja, etc.) |
Getting started 🚀
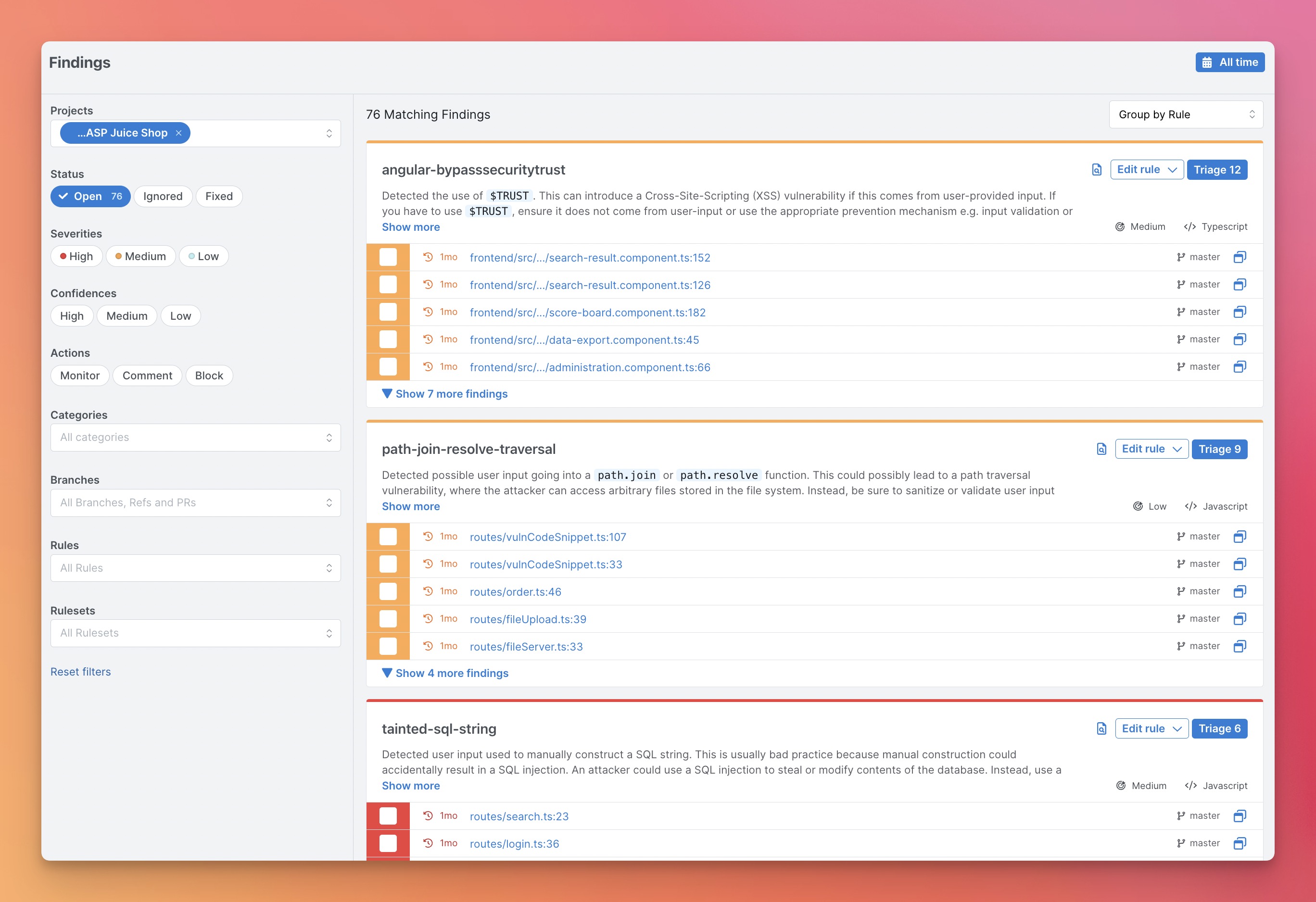
For beginners, we recommend starting with the Semgrep Cloud Platform because it provides a visual interface, a demo project, result triaging and exploration workflows, and makes setup in CI/CD fast. Scans are still local and code isn't uploaded. Alternatively, you can also start with the CLI without logging in and navigate the terminal output to run one-off searches.
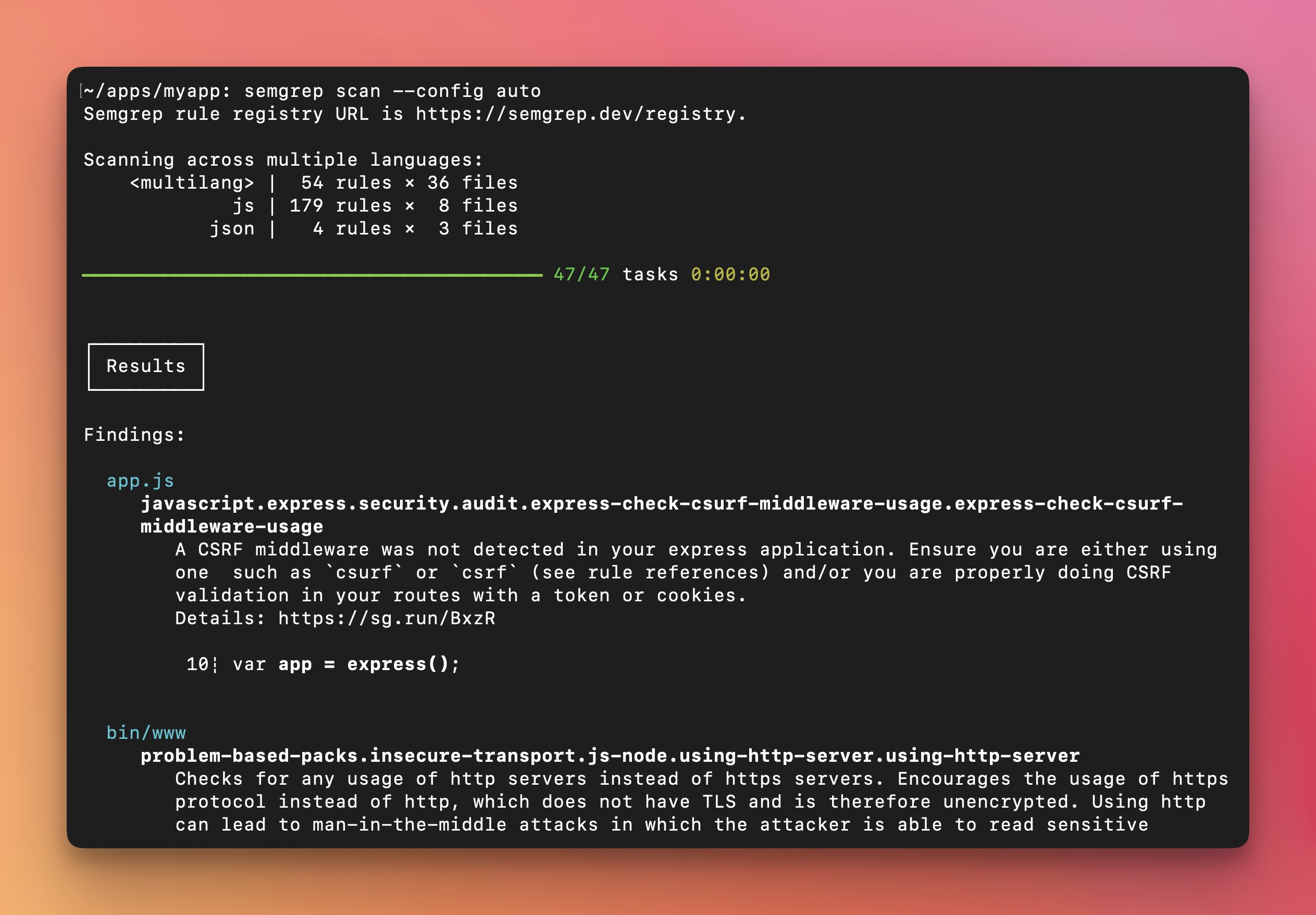
Option 1: Getting started from the CLI
- Install Semgrep CLI
# For macOS
$ brew install semgrep
# For Ubuntu/WSL/Linux/macOS
$ python3 -m pip install semgrep
# To try Semgrep without installation run via Docker
$ docker run --rm -v "${PWD}:/src" returntocorp/semgrep semgrep
-
Go to your app's root directory and run
semgrep scan --config auto. This will scan your project with the default settings. -
[Optional, but recommended] Run
semgrep loginto get the login URL for the Semgrep Cloud Platform. Open the login URL in the browser and login.
Option 2: Getting started from the Semgrep Cloud Platform (Recommended)
-
Register to semgrep.dev
-
Explore the demo app
-
Scan your project by navigating to
Projects > Scan New Project > Run scan in CI -
Select your version control system and follow the wizard to add your project. After this setup, Semgrep will scan your project after every pull request.
-
[Optional but recommended] If you want to run Semgrep locally, follow the steps in the CLI section.
Notes:
-
Visit Docs > Running rules to learn more about
autoconfig and other rules. -
If there are any issues, please ask us at our Slack channel https://go.semgrep.dev/slack
-
To run Semgrep Supply Chain, contact the Semgrep team. Visit the full documentation to learn more.
Semgrep Ecosystem
The Semgrep ecosystem includes the following products:
- Semgrep OSS Engine - The open-source engine at the heart of everything (this project).
- Semgrep Cloud Platform (SCP) - Deploy, manage, and monitor SAST and SCA at scale using Semgrep, with free and paid tiers. Integrates with continuous integration (CI) providers such as GitHub, GitLab, CircleCI, and more.
- Semgrep Code - Scan your code with Semgrep's Pro rules and Semgrep Pro Engine to find OWASP Top 10 vulnerabilities and protect against critical security risks specific to your organization. Semgrep Code provides both Community (free) and Team (paid) tiers.
- Semgrep Supply Chain (SSC) - A high-signal dependency scanner that detects reachable vulnerabilities in open source third-party libraries and functions across the software development life cycle (SDLC). Semgrep Supply Chain is available on Team (paid) tiers.
and:
- Semgrep Playground - An online interactive tool for writing and sharing rules.
- Semgrep Registry - 2,000+ community-driven rules covering security, correctness, and dependency vulnerabilities.
Join hundreds of thousands of other developers and security engineers already using Semgrep at companies like GitLab, Dropbox, Slack, Figma, Shopify, HashiCorp, Snowflake, and Trail of Bits.
Semgrep is developed and commercially supported by r2c, a software security company.
Semgrep Rules
Semgrep rules look like the code you already write; no abstract syntax trees, regex wrestling, or painful DSLs. Here's a quick rule for finding Python print() statements.
Run it online in Semgrep’s Playground by clicking here.
Examples
Visit Docs > Rule examples for use cases and ideas.
| Use case | Semgrep rule |
|---|---|
| Ban dangerous APIs | Prevent use of exec |
| Search routes and authentication | Extract Spring routes |
| Enforce the use secure defaults | Securely set Flask cookies |
| Tainted data flowing into sinks | ExpressJS dataflow into sandbox.run |
| Enforce project best-practices | Use assertEqual for == checks, Always check subprocess calls |
| Codify project-specific knowledge | Verify transactions before making them |
| Audit security hotspots | Finding XSS in Apache Airflow, Hardcoded credentials |
| Audit configuration files | Find S3 ARN uses |
| Migrate from deprecated APIs | DES is deprecated, Deprecated Flask APIs, Deprecated Bokeh APIs |
| Apply automatic fixes | Use listenAndServeTLS |
Extensions
Visit Docs > Extensions to learn about using Semgrep in your editor or pre-commit. When integrated into CI and configured to scan pull requests, Semgrep will only report issues introduced by that pull request; this lets you start using Semgrep without fixing or ignoring pre-existing issues!
Documentation
Browse the full Semgrep documentation on the website. If you’re new to Semgrep, check out Docs > Getting started or the interactive tutorial.
Metrics
Using remote configuration from the Registry (like --config=p/ci) reports pseudonymous rule metrics to semgrep.dev.
Using configs from local files (like --config=xyz.yml) does not enable metrics.
To disable Registry rule metrics, use --metrics=off.
The Semgrep privacy policy describes the principles that guide data-collection decisions and the breakdown of the data that are and are not collected when the metrics are enabled.
More
- Frequently asked questions (FAQs)
- Contributing
- Build instructions for developers
- Ask questions in the r2c Community Slack
- CLI reference and exit codes
- Semgrep YouTube channel
- License (LGPL-2.1)
Upgrading
To upgrade, run the command below associated with how you installed Semgrep:
# Using Homebrew
$ brew upgrade semgrep
# Using pip
$ python3 -m pip install --upgrade semgrep
# Using Docker
$ docker pull returntocorp/semgrep:latest
Project details
Release history Release notifications | RSS feed
Download files
Download the file for your platform. If you're not sure which to choose, learn more about installing packages.
Source Distribution
Built Distributions
File details
Details for the file semgrep-1.16.0.tar.gz.
File metadata
- Download URL: semgrep-1.16.0.tar.gz
- Upload date:
- Size: 284.3 kB
- Tags: Source
- Uploaded using Trusted Publishing? No
- Uploaded via: twine/4.0.2 CPython/3.9.16
File hashes
| Algorithm | Hash digest | |
|---|---|---|
| SHA256 | a480a880cee2953e68ae828726399d1aaabffe3489219e30af609ccc72e8ed2d |
|
| MD5 | 8d3866530ad8af5825526d125b7666b4 |
|
| BLAKE2b-256 | 4783c90088cb1bac530dd9cc280fa3a6eac8a577e7aff89762f41f73028d9dd2 |
File details
Details for the file semgrep-1.16.0-cp37.cp38.cp39.py37.py38.py39-none-macosx_11_0_arm64.whl.
File metadata
- Download URL: semgrep-1.16.0-cp37.cp38.cp39.py37.py38.py39-none-macosx_11_0_arm64.whl
- Upload date:
- Size: 25.7 MB
- Tags: CPython 3.7, CPython 3.8, CPython 3.9, Python 3.7, Python 3.8, Python 3.9, macOS 11.0+ ARM64
- Uploaded using Trusted Publishing? No
- Uploaded via: twine/4.0.2 CPython/3.9.16
File hashes
| Algorithm | Hash digest | |
|---|---|---|
| SHA256 | 397f1ede96a66532922525663efba27be9f63ff0370182865ff7df1ab9edac9e |
|
| MD5 | 04160636a1feb95fd13ee0dbaf52e7a1 |
|
| BLAKE2b-256 | b497e4b2e99fcd4a44c0f093ca9092569a5c530888d2315e291291338a818339 |
File details
Details for the file semgrep-1.16.0-cp37.cp38.cp39.py37.py38.py39-none-macosx_10_14_x86_64.whl.
File metadata
- Download URL: semgrep-1.16.0-cp37.cp38.cp39.py37.py38.py39-none-macosx_10_14_x86_64.whl
- Upload date:
- Size: 22.3 MB
- Tags: CPython 3.7, CPython 3.8, CPython 3.9, Python 3.7, Python 3.8, Python 3.9, macOS 10.14+ x86-64
- Uploaded using Trusted Publishing? No
- Uploaded via: twine/4.0.2 CPython/3.9.16
File hashes
| Algorithm | Hash digest | |
|---|---|---|
| SHA256 | 7b1f0a037849fda5d80c06ab36bf6b5c427d975b211d10c4c7c7fe1a7927d597 |
|
| MD5 | 424e5b0bdcc3b9047d9c0c2f4db1a143 |
|
| BLAKE2b-256 | b0d43400031af05481b98119b338e9b91ba083df9ab058539898e490b02700f4 |
File details
Details for the file semgrep-1.16.0-cp37.cp38.cp39.py37.py38.py39-none-any.whl.
File metadata
- Download URL: semgrep-1.16.0-cp37.cp38.cp39.py37.py38.py39-none-any.whl
- Upload date:
- Size: 25.6 MB
- Tags: CPython 3.7, CPython 3.8, CPython 3.9, Python 3.7, Python 3.8, Python 3.9
- Uploaded using Trusted Publishing? No
- Uploaded via: twine/4.0.2 CPython/3.9.16
File hashes
| Algorithm | Hash digest | |
|---|---|---|
| SHA256 | 83fafcea96100ab1051c153ae0b144dc9a73f5f1cc2cc8bd11d486b4e9688271 |
|
| MD5 | fee1b9ebdcbc428fc6098585a1e1c7e8 |
|
| BLAKE2b-256 | 446beb81626dcdf60452d0f3d9fa8c856866f7edd33bc7f6e8ab978c249f6304 |